Cyber-security is a hot topic, and for good reason. Small and medium-sized businesses often, mistakenly, think they’re safe. Find out why upgrading to Windows 10 should be a top priority.
As a business owner, the decisions you make could determine the future of your business. Like upgrading your operating system. Using out-of-date software could leave your business more vulnerable to cyber attacks, viruses and data theft.
Did you know 43% of all cyber-attacks target small and medium-sized businesses because they tend to be less secure than enterprise companies?
Or that over 300k malware samples specifically designed to damage or gain access to peoples’ computer systems are being created and spread every day?
Threats like these mean your staff could share confidential information without even knowing. In fact, 87% of senior management have leaked data accidentally.
Wake up to a smarter way of protecting your business
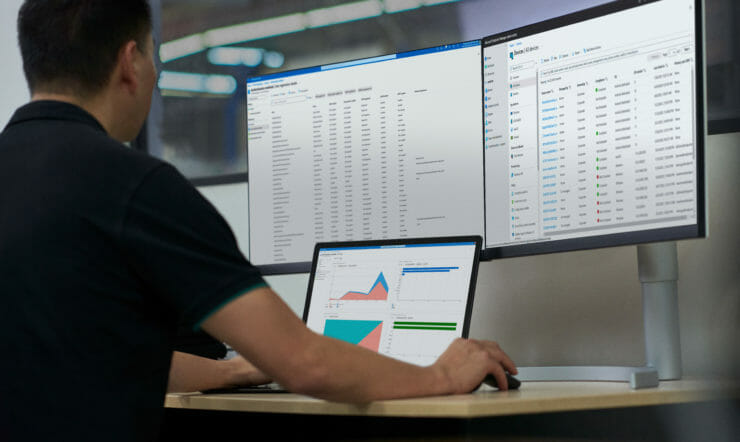
A lot has changed in the world since the release of Windows 7. Operating systems have come a long way too. Take Windows 10 for example. It’ll be the last version – as Microsoft will update it automatically every 6 months. Think of it as service that’ll continue to change, grow and adapt in tandem with your business.
The main features of Windows 10 for business include:
- It’s integrated for simplicity meaning it’s always up-to-date and made easy for all your staff to use and manage
- It has intelligent security with threat protection, built-in antivirus, security management tools and identity protection. In other words, Windows 10 is the most secure release of Windows, ever.
- The productive experience by unlocking creativity and teamwork – empowering every employee to do their best work